H1, 2024 Healthcare Data Breach Report
Several major healthcare cyberattacks have been reported in the first half of 2024, including a ransomware attack on Ascension that took its electronic medical record system out of action for a month and a ransomware attack on Change Healthcare that caused massive disruption for providers across the country due to the unavailability of Change Healthcare’s platform. The amount of data stolen in the Change Healthcare attack is eye-watering, potentially the protected health information of 1 in 3 Americans – More than 110 million individuals.
While these two data breaches could both be massive, at the time of publication, the scale of these data breaches has still not been confirmed. The Ascension data breach was reported to the HHS’ Office for Civil Rights (OCR) in July 2024 and only with a placeholder of 500 individuals due to the ongoing investigation, and while Change Healthcare has started sending notification letters, the breach has yet to be reported to OCR.
About Our H1, 2024 Healthcare Data Breach Report
The data on which our H1, 2024 Healthcare Data Breach Report is based includes healthcare data breaches of 500 or more records that were reported to OCR between January 1, 2024, and June 30, 2024. The data were obtained from OCR on July 23, 2024, to allow OCR time to process reports and add entries to its breach portal. On July 23, there were 32 breaches of 500 or 501 records in the dataset. These figures are commonly used placeholders to meet the HIPAA Breach Notification Rule reporting requirements when the breach investigation has not yet concluded. The total number of affected individuals could increase considerably when these investigations conclude. This report only includes data on large healthcare data breaches that involved the protected health information (PHI) of 500 or more individuals. Smaller data breaches, which typically outnumber larger breaches at a rate of around 100-1, are not made public by OCR, and are therefore outside the scope of this report.
Healthcare Data Breaches Up Year-Over-Year
In H1, 2024, 387 data breaches of 500 or more records were reported to OCR, which represents an 8.4% increase from H1, 2023, and a 9.3% increase from H1, 2022. The first half of the year has seen data breaches reported to OCR in very similar numbers to H2, 2023 when 385 large data breaches were reported. This, together with only modest increases in breaches over the past few years (see our data breach statistics page), suggests that the healthcare industry is starting to turn the corner and the large annual increases in data breaches may have come to an end.
H1, 2024 Sees a Reduction in Breached Records
There has been a 9.5% year-over-year fall in the number of breached healthcare records, with 45,555,982 breached records confirmed in the first half of the year, compared to 50,340,795 records in H1, 2023; however, the first half of 2024 saw 87.8% more records breached than H1, 2022, and 48.1% more breached records than H1, 2021.
The first half of the year did see a 51.6% reduction in breached records from H2, 2024 when 94,091,862 healthcare records were reported as exposed, stolen, or impermissibly disclosed; however, it would have been a very different story if the February 2024 Change Healthcare data breach had been disclosed within the 60 days required by the HIPAA Breach Notification Rule. Our end-of-year report in January 2025 will likely show 2024 to be the worst-ever year for breached healthcare records by some margin, with the Change Healthcare breach likely to be substantially worse than the Anthem Inc. data breach in 2025 that affected 78.8 million individuals.
Causes of H1, 2024 Healthcare Data Breaches
OCR reports that there was a 93% increase in large data breaches from 2018 to 2023, a 239% increase in hacking-related incidents over that period, and a 278% increase in healthcare ransomware attacks. In 2023, hacking-related incidents accounted for 77% of all healthcare data breaches, compared to 49% of data breaches in 2009.
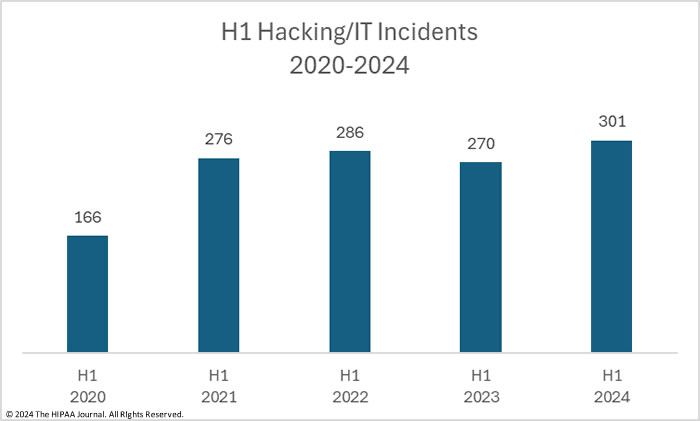
H1, 2024 Hacking/IT Incidents
Hacking/IT incidents cover a broad range of incidents, including hacks, ransomware, malware, and phishing attacks. In H1, 2024, 301 of the 387 large data breaches were hacking/IT incidents and accounted for 77.78% of the January to June total. While the percentage of breaches due to hacking is relatively unchanged from 2023, the number of incidents is up 11.48% from H1, 2023, and 5.2% from H1, 2022, although down 8.0% from the 327 hacking/IT incidents reported in H2, 2024.
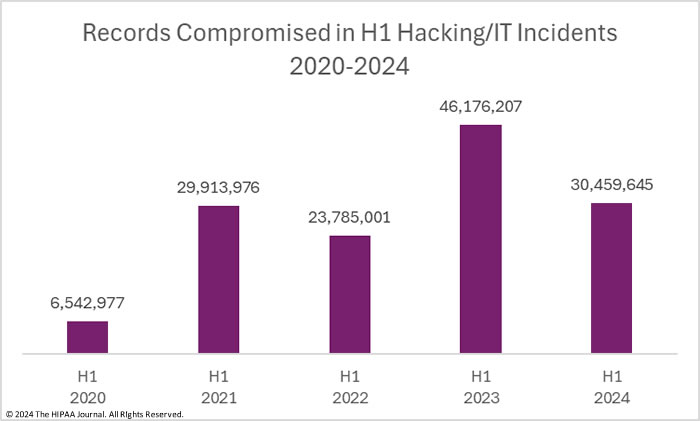
Hacking/IT incidents are up, but the severity of those incidents is down, again with the caveat that the Change Healthcare data breach has yet to be reported. Across those 301 incidents, the PHI of 30,459,645 individuals was exposed or stolen, which is a 34.0% reduction in breached records from Q1, 2023, and a 66.1% reduction from the 89,744,765 healthcare records that were breached in hacking/IT incidents in H2, 2023. In H1, 2024, the average size of a hacking/IT incident breach was 101,195 records and the median breach size was 5,445 records, down from a 171,023-record average in H1, 2023 and an H1, 2023 median of 8,477 records, and a 274,449-record average and a 9,240-record median breach size in H2, 2023.
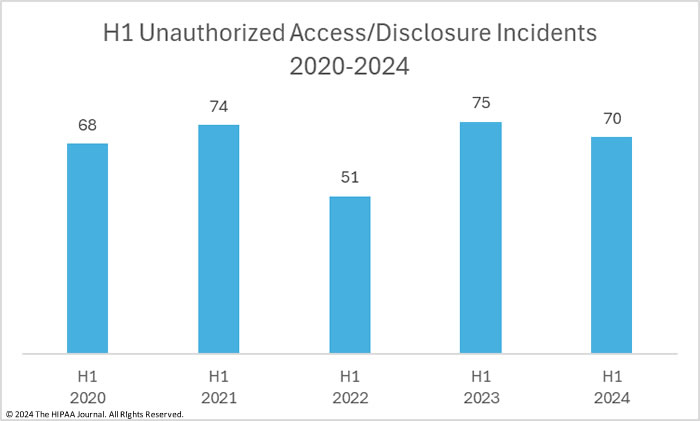
H1 Unauthorized Access/Disclosure Incidents
Unauthorized access/disclosure incidents include unauthorized access to healthcare records by employees or third parties that do not have the authority to access them, accidental disclosures of PHI such as mismailing incidents and misdirected emails, and the exposure of sensitive data online, such as data stored in the cloud without access controls.
Aside from a blip in H1, 2022, unauthorized access/disclosure incidents have been reported at a fairly consistent level over the past five years. While these incidents account for far fewer data breaches than hacking/IT incidents, they can be just as harmful as hacking incidents, if not more. In the first half of the year, 70 incidents were reported, accounting for 18.1% of all H1 data breaches. While there has been a 6.7% reduction in reported incidents from H1, 2023, these incidents are up 40% from the 50 reported incidents in H2, 2023.
Unauthorized access/disclosure incidents tend to involve relatively few healthcare records; however, there was a massive 263.3% year-over-year increase in exposed/disclosed records with 15,027,632 records breached across the 70 incidents. The high number of exposed records was due to a massive breach – the largest confirmed data breach of the year to date – that involved the PHI of 13.4 million individuals.
That breach pushed the average breach size higher than hacking/IT incidents at 214,680 records, although the median breach size was less than half that of hacking/IT incidents at 2,051 records. The average breach size in H2, 2023 for unauthorized access/disclosure incidents was 86,371 records and the median breach size was 1,674 records, and in H1, 2023, the average breach size was 55,155 records and the median breach size was 1,809 records.
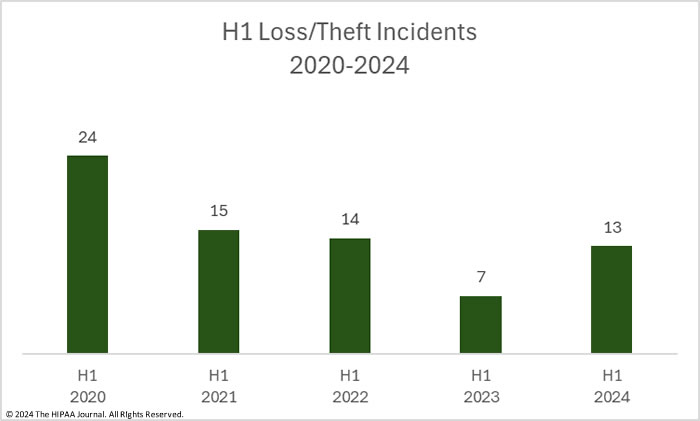
H1 Loss/Theft Incidents
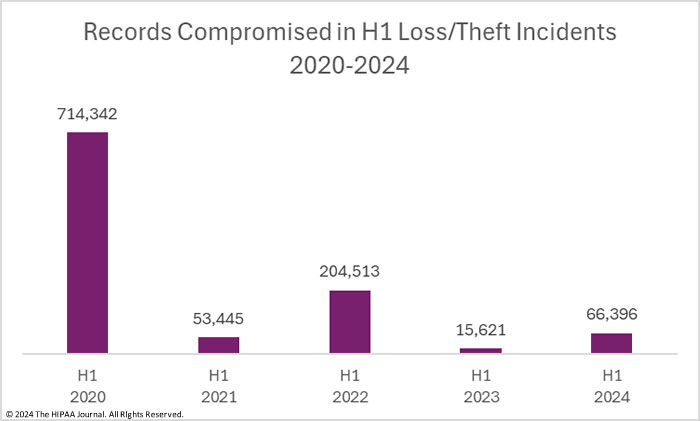
Loss theft incidents include lost or misplaced paper records and lost or stolen electronic devices containing unencrypted ePHI. If a device is lost or stolen and the data stored on the device is encrypted, it is not a reportable data breach unless the means to decrypt the data is also compromised. When OCR first started publishing breach reports, loss/theft incidents were one of the main causes of data breaches but they now occur far less frequently due to more widespread adoption of encryption. In the first half of 2024, there were 13 reports of data breaches involving the loss or theft of electronic devices containing ePHI and paper/records, 85.7% more breaches than in H1, 2023, and 62.5% more breaches than in H2, 2023. More than half (62.5%) of the H1, 2024 loss/theft incidents involved unencrypted laptops and other portable electronic devices.
Loss and theft incidents tend not to involve many records, although loss/theft incidents in H1, 2024 were more severe than in H1, 2023. In the first half of the year, the PHI of 66,396 individuals was exposed or impermissibly disclosed across the 13 incidents, up 325% from H1, 2023, and up 132.4% from the 28,564 records breached in loss/theft incidents in H2, 2023. In H1, 2024, the average breach size was 5,107 records and the median breach size was 3,318 records.
H1 Improper Disposal Incidents
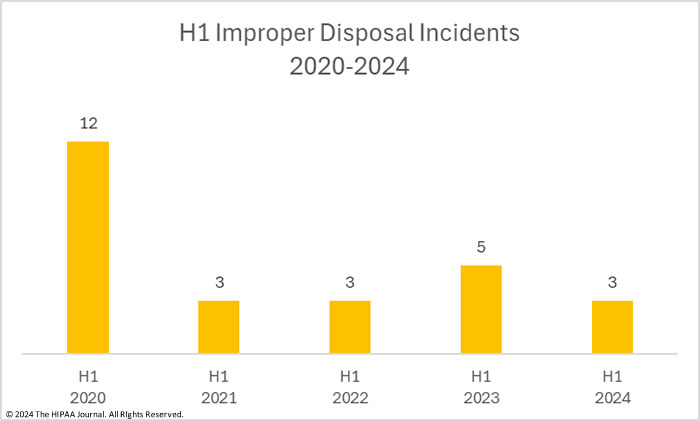
The improper disposal category includes any disposal of PHI or ePHI where the data has not been rendered unreadable, indecipherable, and incapable of being reconstructed. Improper disposal incidents are relatively rare and typically involve employee errors when disposing of paper records. There were 3 improper disposal incidents in H1, 2024, down from the 5 incidents in H1, 2023. There were no reports of improper disposal of ePHI or PHI in H2, 2023.
Across the 3 incidents, the records of 2,309 individuals were exposed or impermissibly disclosed. The average breach size was 770 records, and the median breach size was 568 records, a considerable reduction from the 12,360 records breached in H1, 2023 when the average breach size was 52,472 records and the median breach size was 3,318 records.
Largest Healthcare Data Breaches in H1, 2024
In H1, 2024 there were 7 breaches of 1 million or more records and 39 breaches of more than 100,000 records. The majority of the reported data breaches were relatively small and involved fewer than 10,000 records.
| Individuals Affected | 2024 |
| 500 – 9,999 | 252 |
| 10,000 – 49,999 | 68 |
| 50,000 – 99,999 | 21 |
| 100,000 – 499,999 | 29 |
| 500,000 – 999,999 | 10 |
| 1,000,000 – 4,999,999 | 6 |
| 5,000,000 – 9,999,999 | 0 |
| 10,000,000+ | 1 |
Atypically, the largest breach in the first half of the year was an unauthorized disclosure incident rather than a hacking incident. Kaiser Foundation Health Plan had added tracking technologies to its websites and apps that collected potentially sensitive information of website visitors and transferred that information to third parties such as Google and Meta. There was no business associate agreement between Kaiser Foundation Health Plan and those companies. Kaiser Foundation Health Plan determined that up to 13.4 million visitors to its website and app users may have had sensitive data disclosed by these tools.
Concentra Health Services in Texas was one of many healthcare providers affected by a breach at the transcription services provider, Perry Johnson, and Associates (PJ&A), and was one of the latest to report a data breach. Hackers had access to the PJ&A network for a month in May 2023. PJ&A reported the breach as affecting 8,952,212 individuals; however, several clients, including Concentra, chose to issue their own notifications. The PJ&A data breach was the second largest healthcare data breach last year and affected more than 13 million individuals in total
Sav-Rx in Nebraska experienced a hacking incident that caused network disruption in October 2023 with the investigation confirming there had been data exfiltration. Sav-Rx said the hackers provided proof that the stolen data had not been deleted, indicating the ransom had been paid. WebTPA and Integris Health round out the top 5 and were both victims of hacking incidents involving the theft of millions of healthcare records.
One data breach that stands out was the incident reported by Geisinger, which highlights the importance of terminating access rights promptly when employees leave the company. A business associate used by the firm failed to do that for a terminated employee, who logged in days after termination and accessed millions of Geisinger records.
| Rank | Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Location of Breached Information | Breach Description |
| 1 | Kaiser Foundation Health Plan, Inc. | CA | Health Plan | 13,400,000 | Network Server | Use of website tracking technologies that disclosed PHI to third parties |
| 2 | Concentra Health Services, Inc. | TX | Healthcare Provider | 3,998,163 | Network Server | Cyberattack on business associate, PJ&A |
| 3 | A&A Services d/b/a Sav-Rx | NE | Business Associate | 2,812,336 | Network Server | Cyberattack with data theft |
| 4 | WebTPA Employer Services, LLC | TX | Business Associate | 2,518,533 | Network Server | Hacking incident with data theft confirmed |
| 5 | INTEGRIS Health | OK | Healthcare Provider | 2,385,646 | Network Server | Hacking incident with data theft confirmed |
| 6 | Medical Management Resource Group, L.L.C. | AZ | Business Associate | 2,350,236 | Network Server | Hacking incident with data theft confirmed |
| 7 | Geisinger | PA | Healthcare Provider | 1,276,026 | Network Server | Records accessed by a former employee of a business associate after termination |
| 8 | Eastern Radiologists, Inc | NC | Healthcare Provider | 886,746 | Network Server | Hacking incident |
| 9 | Superior Air-Ground Ambulance Service, Inc. | IL | Healthcare Provider | 858,238 | Network Server | Hacking incident |
| 10 | UNITE HERE | NY | Business Associate | 791,273 | Network Server | Hacking incident |
| 11 | Ann & Robert H. Lurie Children’s Hospital of Chicago | IL | Healthcare Provider | 775,860 | Network Server | Ransomware attack with data theft confirmed |
| 12 | Risas Dental & Braces | PA | Healthcare Provider | 618,189 | Network Server | Hacking incident |
| 13 | Emergency Medical Services Authority | OK | Healthcare Provider | 611,743 | Network Server | Hacking incident |
| 14 | United Seating and Mobility, L.L.C., d/b/a Numotion | TN | Healthcare Provider | 602,265 | Network Server | Ransomware attack with data theft confirmed |
| 15 | Consulting Radiologists LTD. | MN | Healthcare Provider | 583,824 | Network Server | Hacking incident |
| 16 | Group Health Cooperative of South Central Wisconsin | WI | Health Plan | 533,809 | Network Server | Ransomware attack with data theft and ransom demand |
| 17 | North Kansas City Hospital | MO | Healthcare Provider | 502,438 | Network Server | Cyberattack on business associate, PJ&A |
| 18 | Philips Respironics | PA | Business Associate | 457,152 | Network Server | Hacking incident (MoveIT Transfer) |
| 19 | El Centro Del Barrio d/b/a CentroMed | TX | Healthcare Provider | 400,000 | Network Server | Hacking incident with data theft and ransom demand (Karakurt) |
| 20 | Affiliated Dermatologists and Dermatologic Surgeons, P.A. | NJ | Healthcare Provider | 380,000 | Network Server | Hacking incident with data theft and ransom demand |
Location of Breached Protected Health Information
The bar chart below shows where the breached PHI was stored. Unsurprisingly, due to the high number of hacking incidents, network servers were the most common location of breached PHI. Email was the next most common location of breached PHI, but it is reassuring to see the number of email incidents reducing. Email is still a common initial access vector in cyberattacks; however, as more HIPAA-regulated entities implement multi-factor authentication, email accounts become harder to compromise. That said, there was a slight uptick in email incidents in H1, 2024 compared to H1, 2023.
Data Breaches at HIPAA Regulated Entities
The ransomware attack on Change Healthcare caused considerable confusion for the affected covered entities about the breach notification requirements. Following the breach, OCR confirmed that when there is a data breach at a business associate of a HIPAA-covered entity, it is ultimately the responsibility of the covered entity to ensure that individual notifications are issued and the breach is reported to OCR and state Attorneys General; however, the covered entity can delegate the responsibility for issuing notifications to the business associate. If that responsibility is delegated, the covered entity must ensure the business associate fulfills its reporting obligations under HIPAA.
The OCR breach portal lists data breaches by the reporting entity, which may not be the entity that suffered the data breach. As a result, many healthcare data breach reports do not accurately reflect the number of breaches at business associates. The bar charts below show where the breach occurred, rather than the reporting entity.
In H1, 2024, 59% of data breaches occurred at healthcare providers, 39.5% at business associates, 9% at health plans, and 0.6% at healthcare clearinghouses. The above chart shows a steady increase in data breaches at healthcare providers, which are up 9.8% year-over-year and 35.9% higher than H1, 2020 levels. Data breaches at business associates are up 8.5% year-over-year, although there has been a 5.9% reduction in data breaches at health plans.
Even though there were substantially more data breaches at healthcare providers than business associates, more records were compromised at business associates than at healthcare providers, as was the case in H1, 2023. Business associates often provide services to multiple HIPAA-covered entities, so when there is a breach, the records of many entities may be compromised. In H1, 2024, 4 of the top 10 data breaches occurred at business associates.
Geographical Distribution of Healthcare Data Breaches
In H1, 2024, large healthcare data breaches were reported by HIPAA-regulated entities in 45 U.S. states. The only states to make it through the first 6 months of the year with no large data breaches were Alaska, Delaware, Hawaii, Louisiana, South Dakota & Vermont. California was the worst affected state with 38 reported breaches, closely followed by Texas with 34 breaches. These two states also topped the list in terms of breached records, with 14,330,665 and 8,427,581 breached records respectively.
| State | Breaches | Individuals Affected | State | Breaches | Individuals Affected |
| California | 38 | 14,330,665 | Arkansas | 4 | 10,563 |
| Texas | 34 | 8,427,581 | District of Columbia | 4 | 62,781 |
| New York | 26 | 1,474,504 | Nevada | 4 | 50,989 |
| Pennsylvania | 22 | 3,176,221 | New Hampshire | 4 | 38,254 |
| Florida | 21 | 190,624 | New Mexico | 4 | 11,426 |
| Illinois | 18 | 1,926,174 | North Dakota | 4 | 58,422 |
| Ohio | 16 | 163,145 | Oklahoma | 4 | 2,999,236 |
| Massachusetts | 15 | 95,777 | South Carolina | 4 | 14,341 |
| Tennessee | 14 | 685,486 | Virginia | 4 | 88,631 |
| Michigan | 11 | 65,497 | Idaho | 3 | 14,427 |
| Alabama | 10 | 219,737 | Kansas | 3 | 11,600 |
| North Carolina | 10 | 1,341,404 | Missouri | 3 | 513,505 |
| Colorado | 9 | 451,057 | Rhode Island | 3 | 47,607 |
| Arizona | 8 | 2,383,841 | Utah | 2 | 5,119 |
| Indiana | 8 | 442,263 | West Virginia | 2 | 35,806 |
| Kentucky | 8 | 41,849 | Maine | 1 | 500 |
| Washington | 8 | 262,031 | Mississippi | 1 | 170,052 |
| Connecticut | 7 | 152,329 | Montana | 1 | 2,331 |
| Georgia | 7 | 145,373 | Wyoming | 1 | 3,636 |
| New Jersey | 7 | 434,617 | Alaska | 0 | 0 |
| Iowa | 6 | 517,033 | Delaware | 0 | 0 |
| Maryland | 6 | 219,296 | Hawaii | 0 | 0 |
| Oregon | 6 | 11,890 | Louisiana | 0 | 0 |
| Wisconsin | 6 | 713,822 | South Dakota | 0 | 0 |
| Minnesota | 5 | 621,096 | Vermont | 0 | 0 |
| Nebraska | 5 | 2,923,444 |
HIPAA Enforcement Activity in H1, 2024
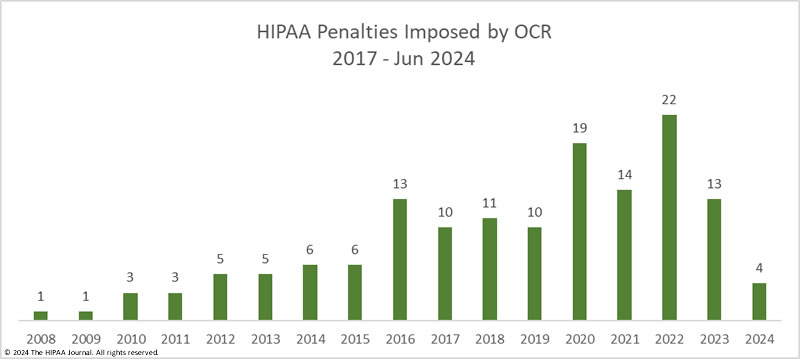
OCR has stepped up its enforcement activities in recent years and has been imposing more financial penalties for HIPAA violations; however, OCR’s resources are strained as its budget has remained flat for years despite its workload increasing. Data breaches are being reported at twice the rate as in 2018, and with no additional funding for OCR, there is naturally a considerable backlog of investigations.
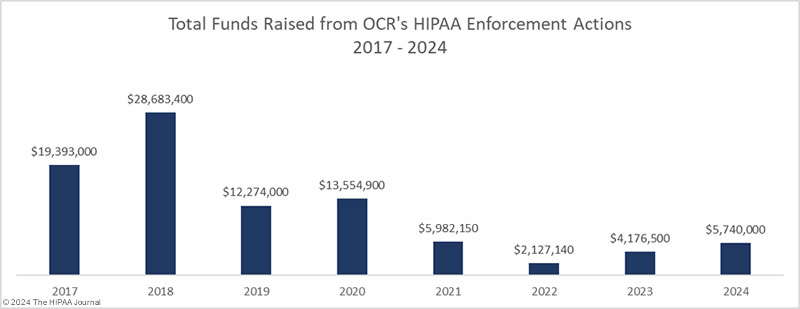
In H1, 2024, OCR fined 4 HIPAA-regulated entities for HIPAA violations and imposed $4,790,000 in financial penalties, a slight increase from H1, 2024. Penalty amounts have reduced significantly in recent years due to the HHS reinterpreting the language of the HITECH Act, which called for increases in penalties for HIPAA violations. As a result, the maximum penalties in three of the four penalty tiers were reduced. OCR has requested Congress increase the penalties for HIPAA violations, so they serve as a bigger deterrent.
In H1, 2024, OCR settled three investigations and imposed one civil monetary penalty. The largest penalty was imposed on Montefiore Medical Center, which chose to settle multiple alleged violations of the HIPAA Rules and agreed to pay a $4,750,000 fine. The data breach that triggered the investigation was relatively small, affecting just 12,517 patients; however, OCR uncovered multiple potential HIPAA violations. The New York hospital system was found to have failed to conduct a comprehensive risk analysis, hadn’t implemented procedures to regularly review records of information system activity, and failed to implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use ePHI.
A civil monetary penalty of $100,000 was imposed on Essex Residential Care (Hackensack Meridian Health, West Caldwell Care Center) for failing to provide an individual with timely access to his mother’s medical records when the son had power of attorney. OCR’s determination was contested; however, an administrative law judge ruled in OCR’s favor. OCR agreed to settle a HIPAA right of access violation for $35,000 with Phoenix Healthcare for failing to provide a daughter with a copy of her mother’s records when the daughter was her mother’s personal representative.
OCR also settled a data breach investigation with Green Ridge Behavioral Health for $40,000. An investigation was launched into a breach of the records of more than 14,000 individuals. OCR determined that Green Ridge had not conducted a risk analysis, failed to manage risks, and had not implemented policies and procedures for reviewing records of information system activity.
OCR is the primary enforcer of HIPAA compliance, although state attorneys general also have the authority to investigate data breaches and issue financial penalties for HIPAA violations. In H1, 2024, state attorneys general settled potential violations of HIPAA and state laws with 4 HIPAA-regulated entities.
The New York Attorney General investigated Refuah Health Center over a breach of the records of 260,740 individuals and determined there had been violations of the HIPAA Security Rule, the Breach Notification Rule, and New York General Business Law related to risk assessments, risk management, reviews of records of system activity, training, and more. Refuah Health Center agreed to pay a $450,000 financial penalty and invest $1.2 million in cybersecurity.
The California Attorney General agreed to settle potential violations of HIPAA and state laws with three HIPAA-regulated entities. Blackbaud was fined $6.5 million for failing to implement reasonable and appropriate cybersecurity measures, making deceptive statements about its security practices, and misrepresentations about its massive 2020 data breach. The $5 million settlement with Quest Diagnostics was primarily for illegally dumping hazardous and medical waste in violation of state laws, but also for violations of HIPAA due to the dumping of unredacted PHI with regular trash. Adventist Health Hanford was investigated over alleged impermissible disclosures of PHI to law enforcement without a warrant and settled for a nominal fine of $10,000.
New Regulations and Cybersecurity Recommendations
This year has seen a final rule issued by OCR to improve reproductive health information privacy. The HIPAA Privacy Rule to Support Reproductive Health Care Privacy final rule prohibits disclosures of an individual’s PHI for the purpose of conducting a criminal, civil, or administrative investigation into or imposing criminal, civil, or administrative liability on any person seeking, obtaining, or facilitating reproductive health care that is lawful in the circumstances it is provided. The final rule took effect on June 25, 2024, and the compliance date for most of the requirements is January 1, 2024.
In December 2023, OCR published its Healthcare Sector Cybersecurity Strategy, which detailed the measures the HHS is taking to improve cybersecurity in the healthcare and public health (HPH) sector, and OCR kicked off the new year with the unveiling of its HPH sector cybersecurity performance goals (CPGs). The HPH CPGs consist of two sets of high-impact measures that the HHS is encouraging HIPAA-regulated entities to adopt to improve resilience to cyber threats and ensure a fast recovery in the event of a successful attack. The goals are mapped to the Health Industry Cybersecurity Practices (HCIP) and the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF).
If the CPGs are widely adopted across the HPH sector, it will make it much harder for hackers to breach healthcare networks, and the high number of breaches we are currently seeing each year should start to reduce. Many HIPAA-covered entities, especially rural hospitals, lack the funds to implement these goals. OCR has submitted a budget proposal for FY2025 that includes $1.3 billion in funds to help under-resourced hospitals adopt the CPGs. OCR has indicated that while the CPGs are voluntary initially, some of the measures will become mandatory in future rulemaking, potentially in a HIPAA Security Rule update that OCR plans to propose by the end of the year.
For some, mandatory cybersecurity measures cannot come quickly enough. Sen. Mark Warner (D-VA) recently wrote to the Department of Health and Human Services (HHS) Secretary Xavier Becerra and Deputy National Security Advisor Anne Neuberger calling for them to quickly develop minimum cybersecurity standards for the healthcare sector due to the extent to which the healthcare industry is being targeted by cybercriminals and nation-state actors and the threat these attacks pose to patient safety. Sen. Warner also introduced the Health Care Cybersecurity Improvement Act of 2024 in response to the Change Healthcare ransomware attack, If passed, healthcare providers will be eligible to receive Medicare accelerated and advance payments in the event of a cyberattack, although only if they achieve minimum standards for cybersecurity.